Browser security standards via access control
时间:2022-03-13 22:59
A computing system is operable to contain a security module within an operating system. This security module may then act to monitor?access?requests by a web browser and apply?mandatory?access?control?security policies to such requests. It will be appreciated that the security module can apply?mandatory?access control?security policies to such web browser?access?attempts.
BACKGROUND OF THE INVENTION
A web browser is a software application for retrieving, presenting, and traversing information resources on the World Wide Web. An information resource is identified by a Uniform Resource Identifier (URI) and may be a web page, image, video, or other piece of content. Hyperlinks present in resources enable users to easily navigate their browsers to related resources.
Original web browsers were static in nature, designed to only render hyperlinked documents in a straightforward manner. Later, scripting protocols such as JavaScript were developed, which allowed scripts to be embedded in the resource to provide simple dynamic functionality, such as user interaction and animated menus. AJAX, which is shorthand for asynchronous JavaScript and Extensible Markup Language (XML) is a group of interrelated web development techniques used on the client-side to create interactive web applications. The use of AJAX techniques has led to a dramatic increase in interactive or dynamic interfaces on web pages.
Today, AJAX applications can rival desktop applications when it comes to speed and performance.
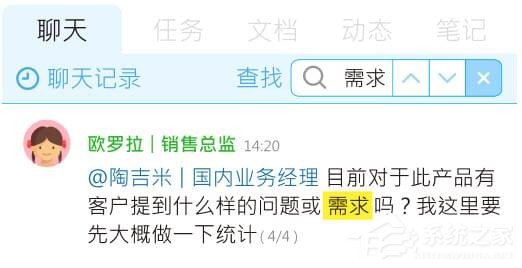
FIG. 1?is a diagram illustrating the operation of a typical web browser. A resource, such as a web page, is downloaded from a web server?100. Images from the web page are separated out by an image separator?102. The web page is then fed to a document object model (DOM) parser?104, which parses the web page into a DOM data structure (commonly referred to as a DOM tree)?106. The DOM tree?106?is an abstract syntax tree of the document. Content referenced by the web page is then fetched from the web server?100?and in-lined into the DOM. As the content necessary to display the page is downloaded and decompressed, the web page becomes available for viewing. Typically the web page layout is incrementally solved and drawn to the screen. A layout module?108?performs the laying out of the elements of the web page, along with images decoded by image decoder?110. A rendering module?112?then renders the web page in the browser window.
After the initial page load, scripts?114?(written in, for example, JavaScript) respond to events (such as events generated by user input or server messages). The scripts can then rewrite the DOM tree?106?based on the events. This, in turn, causes the page layout to be recomputed and redrawn.
The primary use of JavaScript is to write functions that are embedded in web pages and interact with the DOM tree of the page. Typically such scripts are delineated by the <script> and </script> tags. Some examples of script functionality include:
- xshell怎么连接数据库
- MySQL数据库设计规范(仅供参考)
- SQLServer字符串查找(判断字符串是否含数字或字母)
- MySQL源码安装5.7-CentOS7
- 数据库常用架构和同步工作原理
- Apache HBase 1.7.1 发布,分布式数据库
- SQL Server 数据库分离和附加
- sqlSugar 简单封装及使用案例
- 【MySQL】-索引类型
- mysql的数据类型详解
Cookies are handled differently than network accesses. A cookie is a small file stored on a user‘s computer by a web browser and includes one or more name-value pairs containing bits of information such as user preferences, shopping cart contents, the identifier for a server-based session, or other data used by websites. It is sent as an HyperText Transfer Protocol (HTTP) header by a web server to a web browser and then sent back unchanged by the browser each time it accesses that server. A cookie can be used for authenticating, session tracking (state maintenance), and remembering specific information about users, such as site preferences or the contents of their electronic shopping carts.
Rather than the (domain name, protocol, and port number) triple,?accesspermissions for cookies rely on path information. Two paths must be identical in order for the JavaScript running on a web page of the first path to?access?a cookie of a web page of the second path. For example: www.example.com/dir/page.html and www.example.com/dir2/other.html are two different paths and JavaScript running on the first page cannot directly?accessthe cookie of the second, even though they have the same "origin" according to the same origin policy rules outlined above.
Local resources that can be accessed by JavaScript or other web scripting languages include local devices such as Global Positioning (GPS) units, cameras, etc. Such devices are commonplace now on cellular phones, which have now become popular web surfing platforms. The local resources also includes local file systems. W3C does not yet have a set of concrete?access?control?rules for these types of accesses yet.
Existing?access?control?checks are performed inside the web browser application itself. In other words, the web browser applications keep track of each page‘s origin, path, etc. and their?access?requests and make security decisions based on this information. This requires that the design of the web browser include security modules to handle such processing, which complicates the browser design. It also creates security problems. If a malicious page or web application can compromise a browser (e.g., via a buffer overflow), it can circumvent these security checks and gain full?access?to all browser data, including cookies or passwords of other pages. This would then also allow the malicious page or web application to?accessthe local resources, which can have a devastating effect on the functioning of the user‘s device and compromise the user‘s privacy.
Plug-in support mechanisms cause additional security issues in browsers. A plug-in (also called a plugin, addin, add-in, addon, add-on, snap-in, or snapin) is a computer program that interacts with a host application (a web browser or email client, for example) to provide a certain, usually very specific, function on demand. Common plug-ins include Flash, QuickTime, Silverlight, etc.
Plug-ins run in the same address space as the web browser. Thus, there is no distinction between the primary browser code and the plug-in in terms of capabilities. In other words, a plug-in can?access?every system resource that a browser canaccess, including cookies, password files, and local resources. Since plug-ins are usually created and/or distributed by third-parties (i.e., parties other than the creator of the web browser), the threat that malicious code can be imported into the browser code via a plug-in is very high, as users aren‘t always as careful as they should be about which plug-ins they install.
SUMMARY OF THE INVENTION
Broadly speaking, the invention relates to computing systems and computing environments. More particularly, the invention pertains to techniques for applying?access?control?techniques to web browsers. Specifically, such?access?control?techniques may be applied in the operating system.
A computing system can be operable to contain a security module within an operating system. This security module may then act to monitor?access?requests by a web browser and apply security policies to such requests. It will be appreciated that the security module can apply?access?control?security policies to such web browser?access?attempts.
When an operating system service request is received from an instance of a web browser, hooks in the operating system kernel may act to invoke the security module. This invocation might occur just prior to, or simultaneously with, the running of the operating system service request. The security module may then retrieve a security context related to the resource to which the operating system service request is attempting to?access. This security context may then be used to apply anaccess?control?security policy based upon the security context and based upon information regarding the instance of the web browser. The security policy grants?access?to the resource if a property or properties of the security context match a property or properties of the instance of the web browser.
The storage of the security context in the operating system may be accomplished via various different embodiments. In one embodiment, the security context is stored using an extension to an existing file stored in a file system of a kernel of the operating system. In another embodiment, the security context is stored as a stand-alone file in a file system of the kernel of the operating system. In another embodiment, the security context is partially stored using an extension to an existing file stored in a file system of the kernel of the operating system, and partially stored as a stand-alone file in the file system.
The security policy itself may vary in what it allows. In one embodiment, if the resource is a cookie file, then the security policy is a same path security policy. In other words, if the resource is a cookie file, then the cookie file associated with a script located at one path can only be accessed by requesters sharing the same path. In another embodiment, if the resource is a network?access, then the security policy is a same origin security policy. In other words, if the resource is a network?access, then the resource can only be accessed by requestors sharing the same origin.
The invention can be implemented in numerous ways, including, for example, a method, an apparatus, a computer readable (and/or storable) medium, and a computing system (e.g., a computing device). A computer readable medium can, for example, include and/or store at least executable computer program code stored in a tangible form. Several embodiments of the invention are discussed below.
Other aspects and advantages of the invention will become apparent from the following detailed description, taken in conjunction with the accompanying drawings, illustrating by way of example the principles of the invention.
BRIEF DESCRIPTION OF THE DRAWINGS
The present invention will be readily understood by the following detailed description in conjunction with the accompanying drawings, wherein like reference numerals designate like structural elements, and in which:
FIG. 1?is a diagram illustrating the operation of a typical web browser.
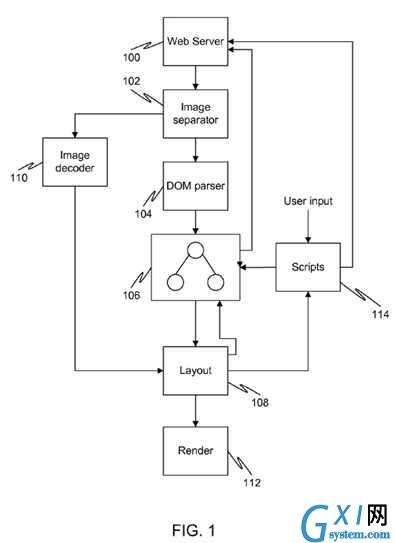
FIG. 2?is a diagram illustrating the overall OP architecture.
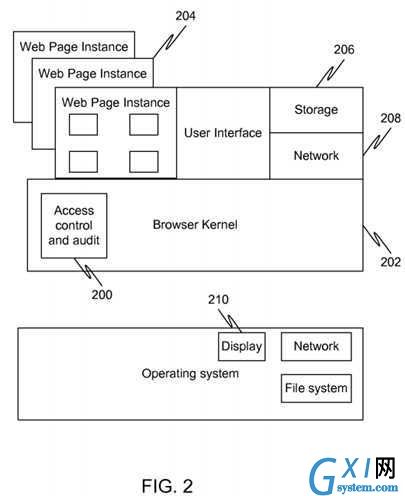
FIG. 3?is a diagram illustrating a web browser architecture in accordance with an embodiment of the present invention.
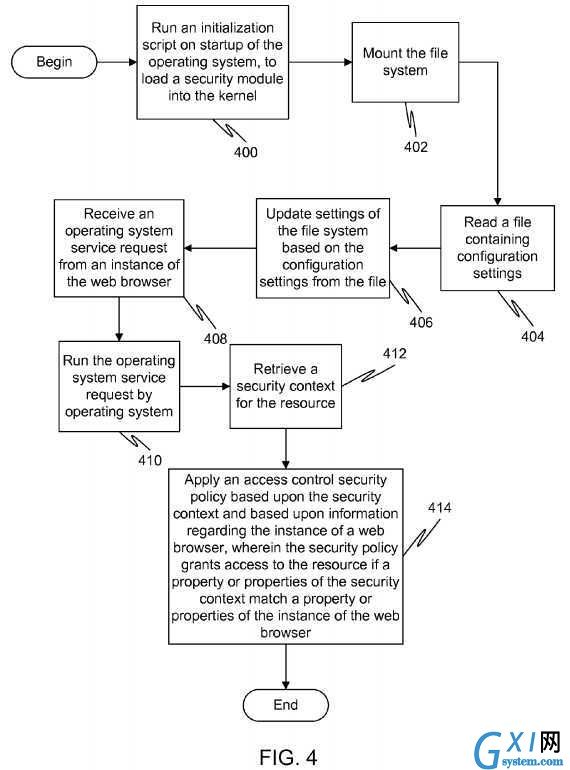
FIG. 4?is a flow diagram illustrating a method for running an operating system in accordance with an embodiment of the present invention.
FIG. 5?is a flow diagram illustrating a method for operating a web browser in accordance with an embodiment of the present invention.
DETAILED DESCRIPTION OF THE INVENTION
As noted in the background section,?access?control?checks are handled inside web browsers. This can create security issues in that a breach of security inside any aspect of the web browser, including plug-in modules that contain third party code, can cause a breach of the entire security of the system. As such, there is the very real danger that resources that should only be available to particular users and/or web browser instances may become accessible to malicious third party users and/or web browser instances.
In an embodiment of the present invention, a separation is created between the monitoring/enforcement of such?access control?checks and the execution of the processes being monitored. This prevents a compromise or corruption in a web browser application from rendering the security mechanisms useless. Resources typically accessible by the executions of the processes are protected from malicious processes by this additional layer of security protection.
In an embodiment of the present invention,?Mandatory?Access?Control?(MAC) or other?access?control?mechanisms are used to overcome the limitations and shortcomings of the prior art. More particularly, the?access?control?checks are performed by an operating system (OS) rather than a web browser. These?access?control?checks may also be performed using MAC mechanisms. This allows a security module of an operating system to monitor the execution of a web browser without a breach of the web browser compromising the security module.
MAC refers to a type of?access?control?where the operating system assigns security labels or classifications to system resources and allows?access?only to entities (people, processes, threads, devices) with distinct levels of authorization. These controls are enforced by the operating system. Whenever an entity attempts to?access?a resource, an authorization rule enforced by the operating system examines these security attributes and decides whether or not to grant the?access. Any operation by the entity on any resource will be tested against the set of authorization rules (also known as policies) to determine if the operation is allowed. The strictness of the security mechanisms makes?mandatory?access?control?quite common in military and other high-security computing systems.
Mandatory?access?control?typically has the security policy centrally controlled by a policy administrator. Individual users typically do not have the ability to override the policy and, for example, grant?access?to files that would otherwise be restricted. This can be contrasted with discretionary?access?control?(DAC).
Discretionary?access?control?is popular in commercial operating systems such as UNIX and Windows. DAC takes a totally different approach, placing?control?of an object into the hands of the person who creates it. For example, if userl creates a file on a Windows server, he becomes the owner of that new file. The owner identification is tracked as part of a security descriptor that the file system maintains for the file. The owner is implicitly granted permission to read the security descriptor and change the?access?control?list for the file.
In other words, discretionary?access?control?means that each object has an owner and the owner of the object gets to choose its?access?control?policy.
Linux is a generic term referring to Unix-like computer operating systems based on the Linux kernel, which was developed as a free and open source software collaboration permitting all the underlying source code to be used, freely modified, and redistributed, both commercially and non-commercially, by anyone under licenses.
Linux has gained popularity for server implementations, however its popularity is also growing on other computing devices, including mobile devices such as mobile phones, laptop computers, etc.
It should be noted that this document will describe the invention as if it is implemented in Linux. While one embodiment is implemented in Linux, nothing in this document or the fact that Linux is described in detail shall be construed as limiting the scope of protection of the patent to Linux embodiments. Indeed, it is foreseen that the present invention could apply to a number of different operating systems.
MAC mechanisms in Linux are implemented through a Linux Security Modules (LSM) framework. LSM is a computing framework for Linux that allows the Linux kernel to support a variety of computer security models while avoiding favoritism toward any single security implementation. LSM was designed to provide everything that is needed to successfully implement an?access?control?module, while imposing the fewest possible changes to the Linux kernel. LSM inserts "hooks", which are upcalls to the LSM, at every point in the kernel where a user-level operating system service request is about to result inaccess?to an important internal kernel object such as inodes and task?control?blocks. An operating system service request is a request that attempts to?access?a resource of the operating system. This request may be, for example, a system call.
An inode stores information about a regular file, directory, or other file system object. This information can include basic details such as user and group ownership,?access?mode (read, write, execute permissions) and type of file, but also could include additional details such as the length of the file in bytes, device identification, file mode, timestamps telling when the inode itself was last changed, the file content last changed, and last accessed, a link count indicating how many hard links point to the inode and pointers to disk blocks that store the file‘s contents.
A task?control?block (TCB), also known as a process?control?block (PCB) is a data structure in the operating system kernel containing the information needed to manage a particular process. This information might include a process identifier, register values, an address space, priority information, process accounting information, a pointer to a next PCB, and I/O information.
LSM provides a general-purpose framework for security that allows security modules to be implemented as loadable kernel modules. Kernel code is modified to invoke hook functions prior to accessing internal objects. Different MAC mechanisms can be implemented as loadable modules. Examples of loadable security modules include SELinux, Smack, and TOMOYO, all of which can be loaded into the kernel on demand.
Each security module registers its own hook functions with the kernel. A kernel data structure, such as security ops, contains function pointers for each hook function. A security module implements some or all of these hook functions, populates the data structure with the pointers to its functions, and then passes this data structure to the kernel for registration. The kernel then asks the security modules, prior to accessing internal objects, for?access?decisions by invoking the appropriate hook function. The security modules can analyze the?access?requests in these hook functions and either permit or prohibit the?access. The kernel is module-agnostic, but provides a powerful framework for modules to operate seamlessly.
OP is a new browser architecture that separates security monitoring mechanisms from the browser instances themselves. Different browsing entities are put in different processes to take advantage of process-level isolation mechanisms.?FIG. 2?is a diagram illustrating the overall OP architecture. As can be seen,?access?control?and auditing?200?can be performed in a browser kernel?202, which is separated from the web page instances?204. In this architecture, storage?control?206, networkcontrol?208, and display?control?210?are put in different processes (subsystems) and separated from the web page or application instances. The browser kernel?202?controls the interactions between these web pages instances?204?and the storage?control?206, network?control?208, and display?control?210?mechanisms.
However, the browser kernel itself is still vulnerable to security breaches as it remains part of the browser. As such, while having the security features located in the browser kernel provides moderate levels of security, especially compared with prior art solutions where the security aspects were managed by the browser instances themselves, the overall vulnerability of the system still remains high.
Therefore, in an embodiment of the present invention, a security module for web browser execution is placed in the operating system, distinct and separate from the web browser instances and the web browser kernel (if any).
Embodiments of these aspects of the invention are discussed below with reference to?FIGS. 3-5. However, those skilled in the art will readily appreciate that the detailed description given herein with respect to these figures is for explanatory purposes as the invention extends beyond these limited embodiments.
FIG. 3?is a diagram illustrating a web browser architecture in accordance with an embodiment of the present invention. As can be seen, an?access?control?module?300?is placed in the operating system?302?itself, distinct from the web page instances?304?or browser kernel?306. By moving the browser-related security features to the operating system, the overall security level of the system is vastly increased, as malicious or corrupt code that has infiltrated the web page instances?304or browser kernel?306?cannot?access?the?access?control?mechanisms and gain?control?of additional resources.
Running the?access?control?module?300?from inside the operating system itself, however, is a non-trivial task. While each web page or application instance can still be run as a separate process, mechanisms must be in place to store browser security related information in the operating system, update such information at runtime, and enforce browser security rules using such information.
Processes and/or threads (i.e., running entities) are "subjects" in?access?control?terms. The Linux kernel keeps records of security properties (also known as the security context) of each process or thread. In other words, each subject has a security context associated with it. The security context of a task is stored in its process?control?block. In the Linux kernel, the process?control?block is called the task struct object.
Each security context can be broken into two categories: the objective context portion and the subjective context portion. The objective context portion of a task includes any portion used when another task is attempting to?access?or affect this task. The subjective context portion of a task include any portion used when the task is attempting to act upon another object (e.g., a file, task, key, etc.).
A task has two security pointers. The first, task->real_cred, points to the objective context portion. The second, task->cred, points to the subjective context portion. These pointers are stored in a task‘s PCB. Additionally, a void pointer, cred->security, is typically provided to allow for custom security credentials. This pointer is commonly used by add-on security modules. For example, SELinux uses its own security credentials and sets cred->security to the structures containing these credentials.
In an embodiment of the present invention, the void pointer is utilized to point to a security module located in the operating system. This allows the security module of the present invention to be easily integrated into a Linux environment with the minimum of complexity.
In addition to altering the pointers so that the security module is referenced, in an embodiment of the present invention the browser related security information is stored in the operating system kernel by the security module.
Keeping records of browser security related information in a security module in the operating system requires mechanisms to store such information. In an embodiment of the present invention, custom data structures are utilized to store such information. While there are a number of different ways such data structures can be implemented, one way is described below.
A novel data structure, called webinstance_browserOS, can be created as follows: